-
 NUAGE PEMF DEVICESPEMF FULL BODY MAT
NUAGE PEMF DEVICESPEMF FULL BODY MAT
PEMF MINIMAT
PEMF RING
PEMF FACE MASK
PEMF PULSEPAD
PEMF MEDALLION
-
-
 Hypertension (high blood pressure)
Hypertension (high blood pressure)
Arrhythmia
Poor blood supply(diabetic foot, ulcer)
Stroke
Parkinson’s disease
Sciatica
Spinal injuries
Multiple sclerosis
Stress
Depression
Fractures
Pseudoarthrosis (nonunion)
Osteoporosis
Osteoarthrosis (osteoarthritis)
Ligament injuries
Frozen shoulder
Tennis or golf elbow
Fibromyalgia
Asthma
Psoriasis
NUAGE PEMF HEAL MEDICAL CONDITIONSMore Medical Conditions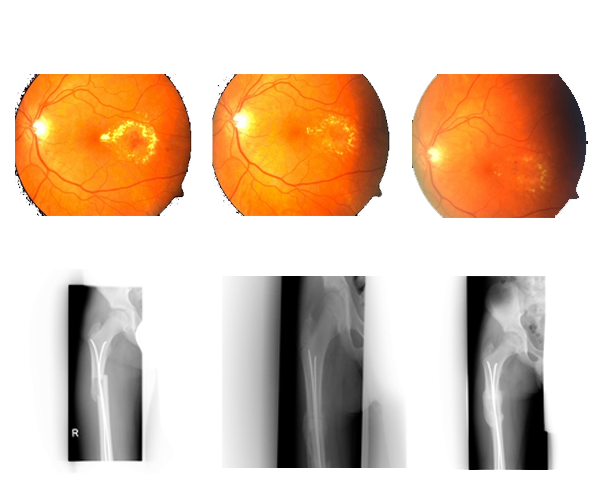 Diabetic RetinopathyFractured Femur & Pelvis
Diabetic RetinopathyFractured Femur & Pelvis
+91 11 4010 9681support@nuagehealth.in162,Chamber -II, Bhikaji Cama Place New Delhi- 110066
7th_april_2022.7z < DELUXE >
: If the file is encrypted, tools like 7z2john are used to extract hashes for brute-forcing with wordlists like rockyou.txt . Static Analysis :
A standard "write-up" for this type of archive typically involves several key stages: : Use 7-Zip or py7zr for Python-based analysis. 7th_April_2022.7z
Recent research (2025/2026) highlights a "Mark-of-the-Web" (MotW) bypass in 7-Zip ( CVE-2025-0411 ), where extracted files lose their "downloaded from internet" security flag, allowing malware like SmokeLoader to run without warnings. : : If the file is encrypted, tools like
: For 2022-dated 7z files, researchers often look for CVE-2022-29072 artifacts, such as malicious .chm (Compiled HTML Help) files used to trigger the "Help > Contents" exploit. Behavioral Observations : : : For 2022-dated 7z files, researchers often
Inspect file headers and metadata to identify the contents (e.g., ELF binaries, scripts, or encrypted payloads).
The file is often associated with cybersecurity research, digital forensics, or historical archive analysis related to vulnerabilities discovered around that date. A significant event for 7-Zip during this period was the disclosure of CVE-2022-29072 , a high-severity vulnerability that allowed for privilege escalation and command execution. Archive Analysis & Write-Up
If this is from a competition, the objective is usually to decrypt a file named flag.txt or reverse-engineer a binary hidden inside the archive. Security Warning





