@redlogsx1.rar | 9500 Logs
At 05:59 AM, as the attacker attempted to initiate the freeze, Kaelen locked them out, the 9,500 logs now serving as the iron-clad evidence of their digital fingerprints. If you want to customize this story, let me know: What of story (thriller, sci-fi, realistic)? Any specific details (names, company, goal)? I can re-write it to fit exactly what you're looking for.
[2026-04-28 03:14:22] - Node 4-Alpha - Traffic Packet 1024/9500 [2026-04-28 03:14:22] - Node 4-Alpha - Anomalous Routing: Packet 1025/9500
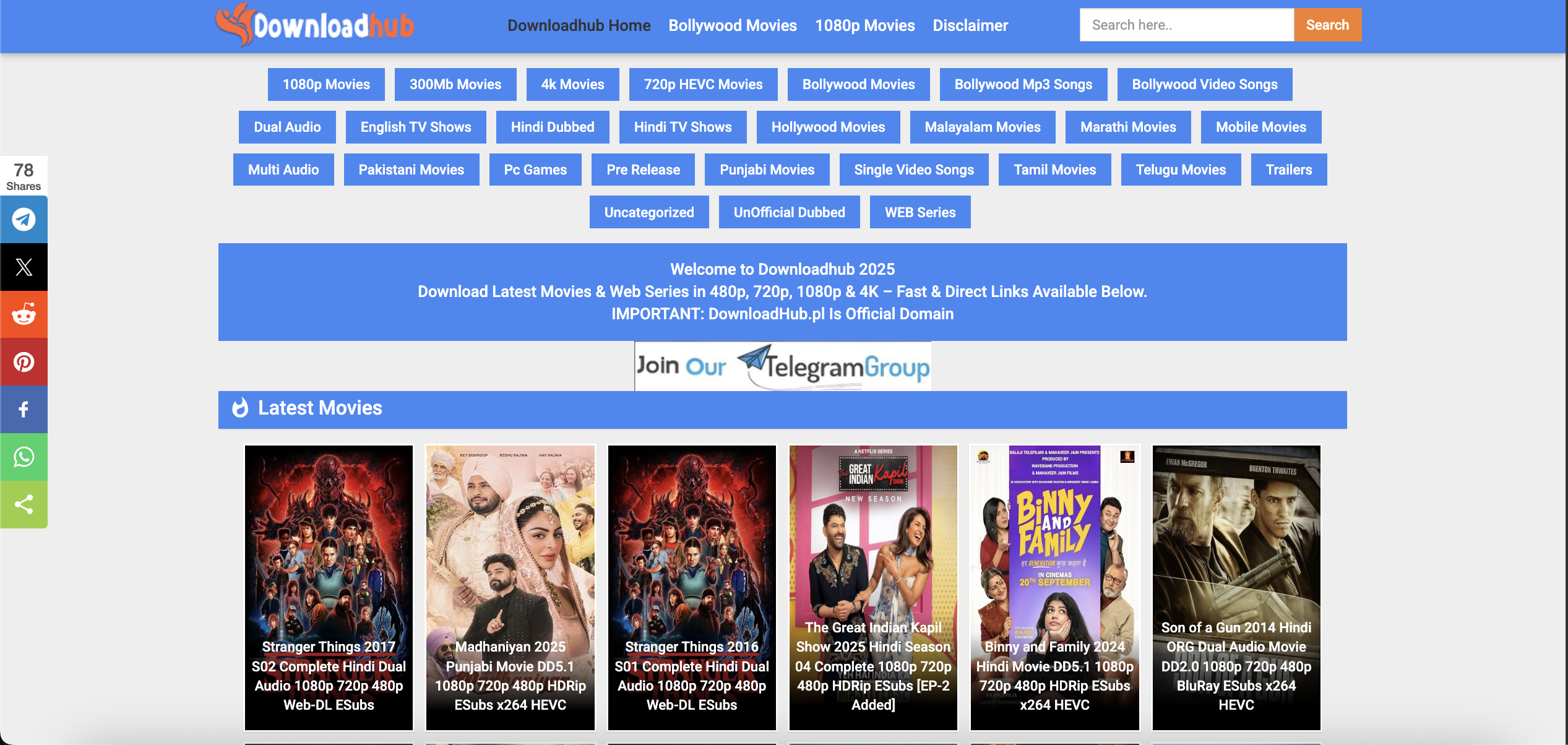
"Show me," Kaelen muttered, typing the command to dump the compressed archive he’d pulled from the perimeter router. unrar x Redlogsx1.rar The screen filled with data. 9,500 logs. 9500 logs @Redlogsx1.rar
The silence in the server room of Aegis Cyber-Defense Solutions was broken only by the low, hypnotic hum of cooling fans. Kaelen Thorne, the firm’s senior forensic analyst, stared at his monitor, his coffee long since gone cold.
"Intelligent," Kaelen murmured, his fingers flying across the keyboard to isolate the file hash. "You want to hide in plain sight with 9,500 entries? I’ll treat them as one." At 05:59 AM, as the attacker attempted to
For three days, the network traffic had been a "ghost" pattern—appearing as legitimate user queries, yet taking impossible routes through the secure mainframe.
It wasn't a standard breach. The attacker wasn't trying to steal data immediately; they were seeding the system, breaking down the firewall’s heuristic AI by flooding it with micro-patterns. The 9,500 logs were not just activity records; they were a digital Trojan horse, designed to trigger a total, catastrophic system freeze at 06:00 AM. I can re-write it to fit exactly what you're looking for
He initiated a rollback, injecting a script that would turn the 9,500 logs into a honeypot, trapping the attacker inside the very data they had used to break in.