IN THE SPOTLIGHT: MDE to MDB Conversion Service
(also supports: ACCDE to ACCDB, ADE to ADP, etc)
IN THE SPOTLIGHT: Access Database Repair Service
An in-depth repair service for corrupt Microsoft Access files
IN THE SPOTLIGHT: vbWatchdog
VBA error handling just got easier...

" vbWatchdog is off the chart. It solves a long standing problem of how to consolidate error handling into one global location and avoid repetitious code within applications. "
- Joe Anderson,
Microsoft Access MVP
Meet Shady, the vbWatchdog mascot watching over your VBA code →
(courtesy of Crystal Long, Microsoft Access MVP)
IN THE SPOTLIGHT: vbMAPI
An Outlook / MAPI code library for VBA, .NET and C# projects
Get emails out to your customers reliably, and without hassle, every single time.
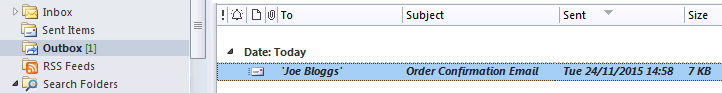
Use vbMAPI alongside Microsoft Outlook to add professional emailing capabilities to your projects.
IN THE SPOTLIGHT: Code Protector
Standard compilation to MDE/ACCDE format is flawed and reversible.
Unlike traditional malware that secretly infects a system, these scams rely on . They often begin when a user visits a "shady" website and accidentally clicks "Allow" on a request to show notifications. Once permission is granted, the attacker can push alerts directly to the user’s desktop or mobile device, even when the browser is closed. These alerts often use alarming language, such as "(5) Virus/Malware infections have been detected," and may even display the user's device name or IP address to appear more legitimate. 2. The Psychology of Urgency and Panic
In the landscape of modern cybersecurity, one of the most persistent and deceptive threats is the technical support scam disguised as an urgent system alert. The specific phrase often appears in malicious browser notifications, designed to trick users into believing their device is infected with multiple threats that require immediate action. 1. Technical Deception via Browser Notifications Download 580K rar
The core of this scam is . By using specific filenames like "580K.rar" or claiming that "5 viruses" have been found, scammers create a sense of technical specificity that can overwhelm non-technical users. They often include countdown timers or loud, alarming sounds to induce panic, hoping the user will "click mindlessly" to resolve the supposed threat. The goal is to drive the victim to download a real malicious file—often a Trojan or infostealer—or to call a fake support number where criminals attempt to gain remote access to the computer. 3. Protection and Mitigation Unlike traditional malware that secretly infects a system,