The first step is to establish the basic identity of the file using cryptographic hashes to ensure it hasn't been tampered with. XXWardinaXX.zip
High, Medium, or Low based on its ability to exfiltrate data or damage the system.
"XXWardinaXX.zip" is not a widely known malware sample or a common public CTF challenge based on available records. If this is a specific file you encountered in a training lab, a local security competition, or a suspicious email, a formal typically follows this structure: 1. File Identification (Triage)
Use a tool like CertUtil (Windows) or sha256sum (Linux) to generate these. FileType: Confirm it is a standard ZIP archive . 2. Static Analysis Examine the file without executing it to avoid infection.
Check if it attempts to contact a Command & Control (C2) server or download additional payloads.
Note if it creates "mutexes," modifies the registry for persistence, or drops new files into C:\Users\ folders. 4. Findings & Summary
High entropy often indicates the contents are encrypted or packed to hide from antivirus software. 3. Dynamic Analysis (Behavioral)
 Бытовые вытяжные вентиляторы
Бытовые вытяжные вентиляторы Вентиляторы для оконно-настенной установки
Вентиляторы для оконно-настенной установки Канальные вентиляторы
Канальные вентиляторы Мультизональные вытяжные вентиляторы
Мультизональные вытяжные вентиляторы Бытовые кухонные вентиляторы
Бытовые кухонные вентиляторы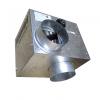 Вентиляторы для распределения теплого воздуха
Вентиляторы для распределения теплого воздуха Бытовые вентиляторы
Бытовые вентиляторы Обогреватели и конвекторы
Обогреватели и конвекторы Фены и сушилки для рук
Фены и сушилки для рук Крышные вентиляторы
Крышные вентиляторы Вентиляторы с EC-двигателями
Вентиляторы с EC-двигателями Осевые вентиляторы с монтажной пластиной
Осевые вентиляторы с монтажной пластиной Осевые вентиляторы в цилиндрическом корпусе
Осевые вентиляторы в цилиндрическом корпусе Струйные вентиляторы
Струйные вентиляторы Вентиляторы в корпусе
Вентиляторы в корпусе Центробежные вентиляторы
Центробежные вентиляторы Пластиковы центробежные вентиляторы
Пластиковы центробежные вентиляторы Воздушные завесы и тепловентиляторы
Воздушные завесы и тепловентиляторы Приточные установки
Приточные установки Приточно-вытяжные установки
Приточно-вытяжные установки